Everyone loves to rave about the benefits of the Internet of Things (IoT). However, few people appreciate the demands IoT systems bring to the table. Cost management and network design are hard enough, but the bulk of IoT field devices operate at minimum power and data flow. Many were deployed in control and automation facilities decades ago and support only simple communication functions. This creates a unique security challenge. IoT can force a designer to incorporate anywhere from hundreds to millions of endpoint devices without being able to secure them on an individual basis. There are many approaches to solving this problem. One feasible solution is to create private networking layers to minimize risk without spending exorbitant amounts on each IoT device.
Total Isolation
When you compare costs and trade-offs for ways to implement an IoT network, most people arrive at the same conclusion: isolation. Consider the extreme case. SCADA, PLCs, sensors and other data collection points in a single production plant could potentially run on a completely private intranet. There are no access points that connect to any other networks, internet or otherwise. Such a design must process all sampled data on site. It eliminates any possibility of remote access, but it creates obstacles for the equipment operating the facility. Worst of all, it doesn’t provide perfect security. Someone in proximity to the network could still exploit any access point to steal data or create harm. That proximity requirement is prohibitive to remote attacks. However, you’re losing a lot of operational efficiency for a security that is strong but not perfect. That leads us to consider another architecture – segmented isolation.
Segmented Isolation
Segmenting a network is a pretty old concept. The idea can be likened to a medieval castle. A layering of walls and defenses enables protocols and countermeasures to respond to network intrusion and mitigate the risk. In simple terms, the concept is outlined in the diagram below.
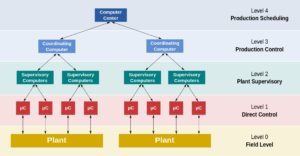
Functional levels of a manufacturing control operation
SCADA, https://en.wikipedia.org/w/index.php?title=SCADA&oldid=852629143
At the base level, you have your IoT collection points. Groups of collection points nested into a private intranet linked are through a single switch, router or firewall. (The APR-3100N from Antaira Technologies is an excellent option for an industrial setting.) If necessary, security may expand by incorporating VPNs or additional segmented layers.

Because none of them directly interact with the core networking infrastructure, you aren’t limited by the security of any single device. You get the benefits of total isolation. But, now you have room to design the networking infrastructure around other needs.
As you can see in the picture, you may add as many layers of security as necessary. From here, the design will defer to your assessment of cost vs. risk. As always, increasing security increases costs which impact efficiency. If every packet travels through dozens of layers of security, you lose real-time interactions. By that same token, some data is worth securing more than others. The value of the information being transmitted and risk to your operation if any one segment is compromised will direct your design. Segmentation offers opportunities to create buffers between vulnerable components and integral systems in a network. There are several ways to utilize segmentation for more robust security.
Analyzing Network Data
The challenges of monitoring segmented networks are the same as providing security to every point on an IoT network. Most of the endpoint devices don’t have enough power to run security or monitoring protocols. The solution is to run them at the level of each segmented node. An intelligent router or firewall will flag anomalous behaviors. The first places to look for unusual changes are in power consumption and traffic data. When suspicious behavior is found, one can merely isolate the affected segment without subjecting the entire system to downtime. Many major security firms and equipment manufacturers such as Cisco offer software to automate such detection.
Out-of-Band Monitoring
A second and valuable layer of security comes from out-of-band monitoring. It circumvents infiltration that could compromise in-band monitoring systems. More importantly, the two (or more) sets of monitoring data may be cross-referenced to ascertain when anomalous network behavior merits intervention. Out-of-band tools can scan outgoing traffic, data exfiltration, and DDoS behavior.
Integrating Components
The primary point of taking extra measures with IoT networking is to account for the variety of IoT devices. Some are entirely self-sufficient and won’t need the additional layers of security. Many others, like legacy IoT 0.9 devices, lack computing, memory, and essential network management. They have no self-sufficiency at all. Enabling your design to accommodate all types of IoT equipment increases options and helps with future proofing. The money spent on segmented security is easily recouped when you have the choice of more affordable IoT integration.
Improved data collection and analysis will grow in most industries. While the range of data you monitor today might be narrow, you can rest assured that those demands will multiply within 20 years. Segmented networks provide a sustainable approach to managing that growth.

Leave a Reply